nginx content security policy header
Hello,
In this post I will share how we can protect our site if we use nginx for a web server.
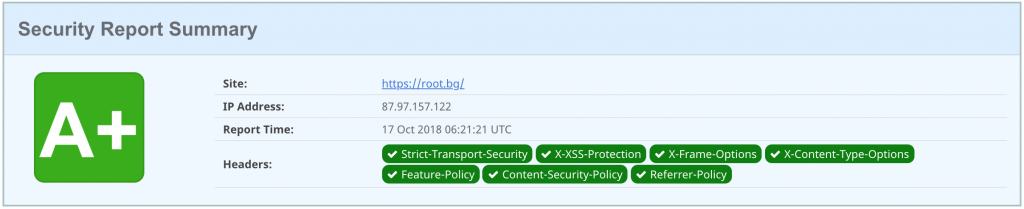
Led by Scott Helme for CSP, I started to test the CSP header of root.bg. I used his securityheaders.com tool and finally achieved the desired result – A + 🙂
nginx content security policy header
In the virtual host of our site we add the following lines after location /
add_header Content-Security-Policy "block-all-mixed-content; frame-ancestors 'self' root.bg cdn.root.bg s.root.bg go.root.bg git.root.bg fonts.gstatic.com;"; add_header Content-Security-Policy-Report-Only "default-src https: data: 'unsafe-inline' 'unsafe-eval'; report-uri https://rootbg.report-uri.com/r/d/csp/reportOnly";
report-uri.com
I made a report on the site report-uri.com and so I started collecting information from my webserver for XSS attacks, web server configuration errors, monitoring and everything else related to the new web standards.
I personally have a bit of luck with the addition of redundant header, but almost all of them are for protection 🙂
HTTP/2 200 date: Wed, 17 Oct 2018 07:13:17 GMT content-type: text/html; charset=UTF-8 vary: Accept-Encoding set-cookie: PHPSESSID=d2lar8sp9vq24752mip9lu31ls; path=/; secure; HttpOnly expires: Thu, 19 Nov 1981 08:52:00 GMT cache-control: no-store, no-cache, must-revalidate pragma: no-cache x-powered-by: 🐧 link: https://root.bg/wp-json/; rel="https://api.w.org/" link: https://go.root.bg/21; rel=shortlink server: rws strict-transport-security: max-age=31536000; includeSubDomains; preload x-cache: HIT x-xss-protection: 1; mode=block; report=https://rootbg.report-uri.com/r/d/xss/enforce x-frame-options: SAMEORIGIN x-content-type-options: nosniff p3p: Can I help you? Contact me via https://root.bg/contacts/, CP=CAO ADMa DEVa IND PHY ONL UNI COM LOC feature-policy: sync-xhr 'self' https://root.bg content-security-policy: block-all-mixed-content; frame-ancestors 'self' root.bg cdn.root.bg s.root.bg go.root.bg git.root.bg fonts.gstatic.com; content-security-policy-report-only: default-src https: data: 'unsafe-inline' 'unsafe-eval'; report-uri https://rootbg.report-uri.com/r/d/csp/reportOnly referrer-policy: no-referrer-when-downgrade expect-ct: enforce; max-age=86400; report-uri=https://rootbg.report-uri.com/r/d/ct/enforce x-app-server: gevi x-slogan: Respect is earned, not given!
Thats it!